Proactive Cybersecurity Risk Management for ASCIP Members
- Home
- Proactive Cybersecurity Risk Management for ASCIP Members

Proactive Cybersecurity Risk Management for ASCIP Members
ASCIP and ResoluteGuard have partnered to deliver a comprehensive cybersecurity program specifically designed to enhance your organization’s cyber posture. Our combined expertise ensures proactive protection and tailored solutions to meet your security needs.
Free Resource Provided by ASCIP
vCISOSecure, easy-to-use Cybersecurity Risk Management tool, designed to empower ASCIP members in strengthening your cyber defenses.
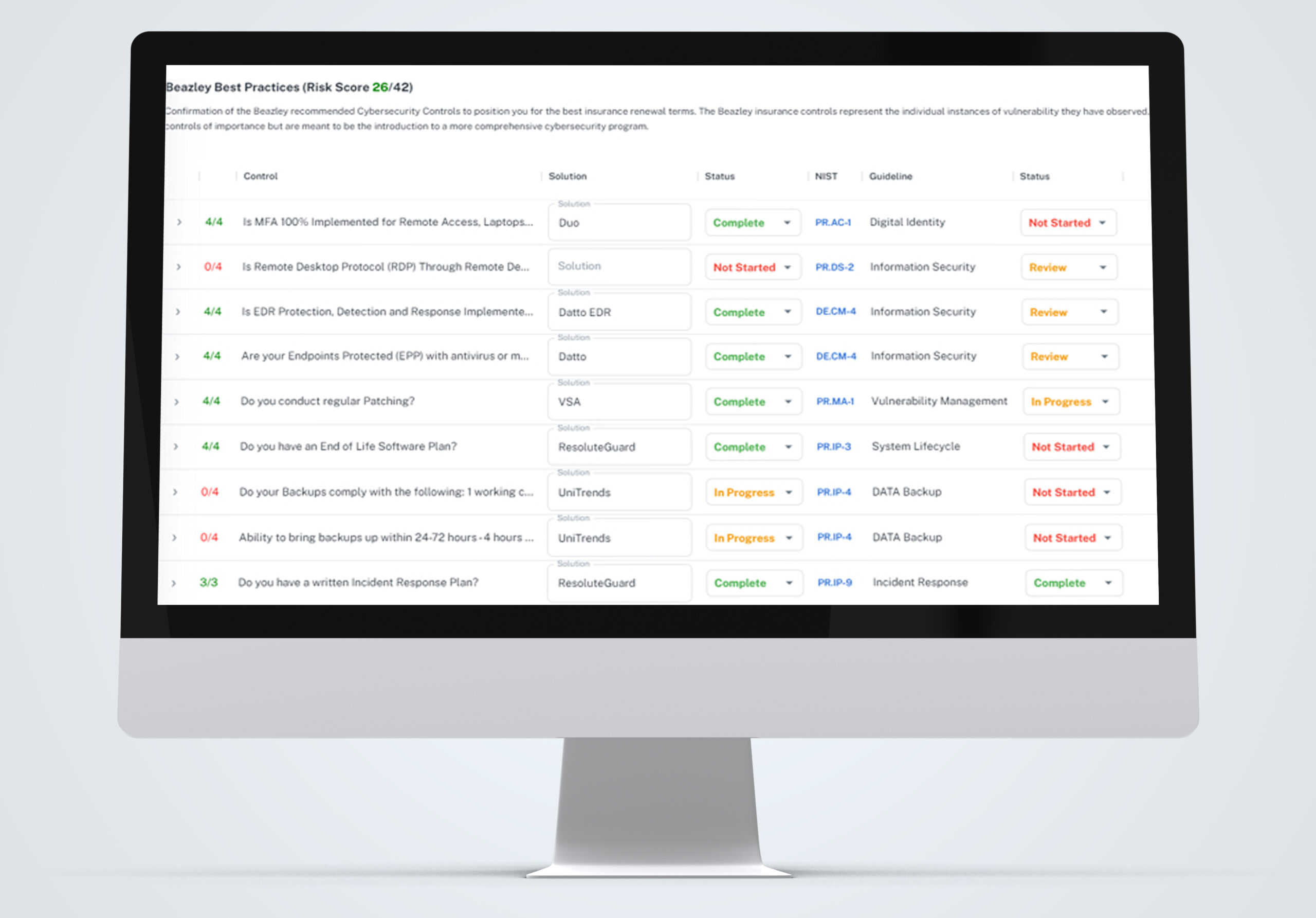
SMART-Cyber Action Plan™
Customized Plan & strategy for ASCIP members aligned with your Beazley’s insurance Cyber Best Practices with a focus on continuous improvement and actionable insights. vCISOSecure ensures you are well-equipped to maintain robust cyber defenses and meet evolving best practices.
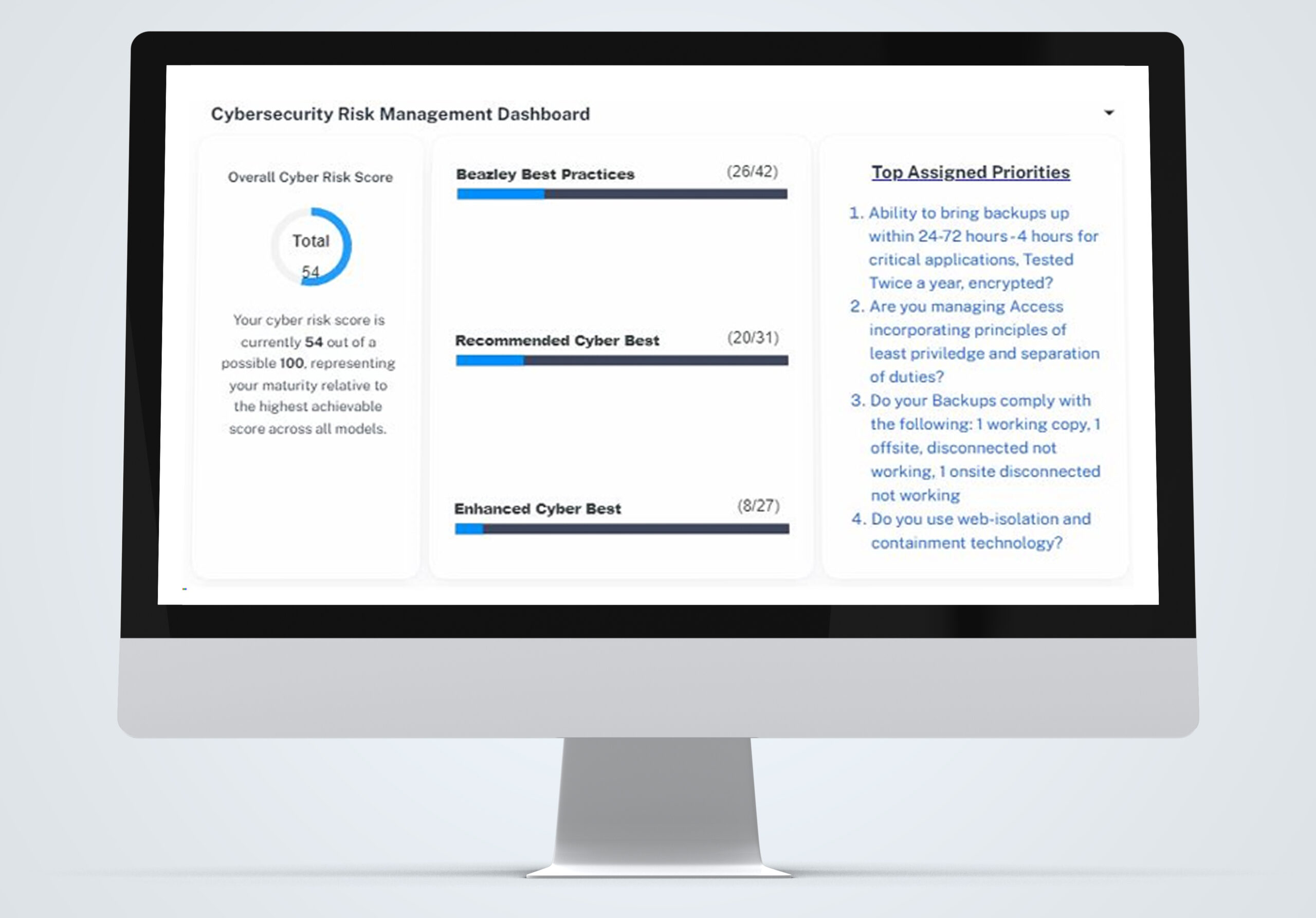
Real-time Dashboard & Cyber Analysis
Provides relevant cyber data to accurately assess your risk offering insights into baseline cybersecurity postures and continuous improvement during the year.

ResoluteGuard’s Cyber Team Knowledge and Guidance
Providing expert cybersecurity guidance to safeguard your organization’s assets and protect against vulnerabilities. This engagement provides expert guidance on your current security posture and delivers critical recommendations to enhance your cybersecurity posture.
Real-time Cybersecurity Risk Management Executive Summary
Provides up-to-date analysis of your current cybersecurity posture, provides a clear overview of cybersecurity risks and statuses, facilitating better communication between IT teams and executive leadership.

Templated Policies & Guidelines (Prioritizing IRP, BCDR, Information Security Policies)
Downloadable Policies and Guidelines provide a significant advantage in developing essential documentation. Policies are essential tools in managing the growing risks of cyber incidents, particularly as public entities become more dependent on digital infrastructure and as cyber threats continue to rise in sophistication and impact.
Here's What You Get with vCISOSecure: Comprehensive Vulnerability Scans & Email Phishing Training
Comprehensive Vulnerability Scans (Internal Network & External)
Comprehensive External AND Internal Network vulnerability scan to identify cyber risks. These comprehensive scans detect and address vulnerabilities before they can be exploited, ensuring a stronger security posture.
Simulated Email Phishing Campaigns
Phishing simulations help your employees recognize common phishing techniques, such as suspicious links, spoofed email addresses, and urgent requests. Training through real-world scenarios increases their ability to spot phishing attempts before they cause harm.
Member Engagement: Simple 4-Step Process
As with any critical process, our first step is meeting to understand your, people, goals, objectives, and priorities. This call is an opportunity for the Executive Leadership and IT Team to meet with ResoluteGuard’s Cyber Risk Coordinator and ensure their mission and goals align to support their plan/strategies. ResoluteGuard’s Cyber Risk Coordinators obtain the information needed to assess technical gaps and risks and update the members’ SMART- Cyber Action Plan.
Program Overview Call
60 Minutes

The Cyber Risk Assessment includes vulnerability scans. These scans help to identify risks such as Common Vulnerabilities and Exposures (CVEs), server misconfigurations, and sensitive data exposures, all of which provide ResoluteGuard and the member with the information essential to developing their Cybersecurity strategy.
Scan Activation Call
30 Minutes

Internal Network and External Vulnerability Scan Reports include a description of Risk findings, recommendations and remedial actions. It prioritizes highest risks by severity and probability. The cyber risk assessment has great value when it provides actionable steps to remediate issues. Several Reports including network documentation (Assets, Users, application inventories, and more) are provided.
Report Review Call
60 Minutes

Additional Services Available at discounted fees for ASCIP members:
Multi-factor Authentication (MFA) – extra layer of security to the authentication process.
Endpoint Detection & Response (EDR) – protect devices such as desktops, laptops, tablets, smartphones, and servers from various cyber threats.
Managed SOC – 24/7/365 monitoring of your network and alert you of potential cyber risks.
Remote Monitoring & Management (RMM)– RMM software allows IT administrators to remotely monitor device health, performance, and security status in real-time. It enables tasks such as software deployment, patch management, system updates, troubleshooting, and remote desktop support.
Mobile Device Management (MDM)– MDM software allows IT administrators to enforce security policies, configure device settings, deploy applications, and remotely manage mobile devices from a centralized console.
Backup & Recovery – ensure data protection, business continuity, and compliance with regulations.
Third Party Risk Management – safeguard against potential risks that arise from partner/vendor/supplier engagement.
Email Security – Email security provides proactive defense mechanisms to prevent attacks before they can cause significant damage.
Want to Learn More?

Email a Cyber Specialist
Speak with a ResoluteGuard specialist to learn how you can improve your cybersecurity posture.

Schedule a Call
Learn in real-time how ResoluteGuard can provide cybersecurity protection.

Give Us a Call!
Can’t wait to speak with us? Give us a call directly to learn how we can improve your cybersecurity posture.

