Do You Have Proper Guidelines in Place When a Cyber Incident Occurs?
Reasonable steps and best practices such as Information Security Policies, Encryption guidelines, Security Awareness training and other measures are implemented to prevent incidents from occurring. However, when an attacker is successful in penetrating the layers of security, a plan of action needs to be predefined to ensure efficient containment and remediation of the event.
An Incident Response Reporting Form is a crucial document used to collect and record detailed information about a security event.
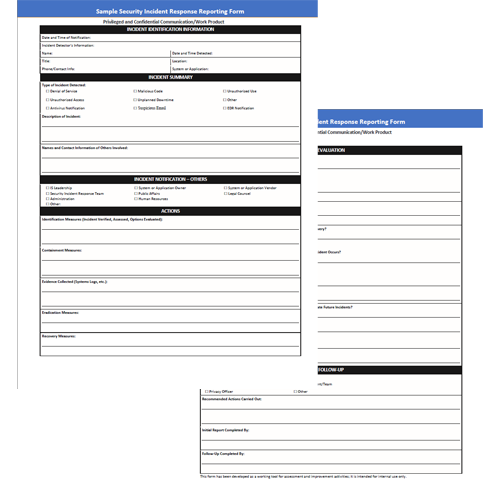
Get Your FREE Incident Response Reporting Form:
Simply fill out the form below:

Event Definition
Any abnormal observable occurrence in system, network, environment, process, workflow, or personnel. Events may or may not be negative in nature.

CRUCIAL FOR CYBERSECURITY
This policy provides the framework to address the six steps necessary to minimize the negative effects of a security breach.
- Preparation
- Identification, Reporting & Assessment
- Containment and Intelligence
- Eradication
- Recovery
- Lessons Learned

Phase I – Preparation Details
The Preparation phase is easily the most important and often overlooked phase. Without proper preparation incident response activities may be disorganized, expensive, and could cause irreparable harm to your organization.
Phase II - Identification, Reporting & Assessment
When an employee or external party notices a suspicious anomaly in data, a system, or the network, or a system alert generates an event, Security Operations, Help Desk, or CSIRT must perform an initial investigation and verification of the event.


Phase III – Containment and Intelligence
The objective of the containment phase of the incident response is to regain control of the situation and limit the extent of the damage. To achieve this objective, the company has defined several containment strategies relevant to a variety of incident types.
Phase IV – Eradication Details
The Eradication consists of full elimination of all components of the incident.

Phase V – Recovery Details
Prior to restoring systems to normal operation, it is critical that the CSIRT validate the system(s) to determine that eradication was successful, and the network is secure. Once the organization has been attacked successfully, the same attackers will often attack again using the same tools and techniques leveraged in the initial attack. Having gained access to the compromised system(s) or network once, the attacker has more information at their disposal to leverage in future attacks.
Phase VI - Lessons Learned
The follow-up phase includes reporting and post-incident analysis on the system(s) that were the target of the incident and other potentially vulnerable systems. The objective of this phase is continued improvement to applicable security operations, response capabilities, and procedures.
Learn how ResoluteGuard can help your organization reduce risk, reduce complexity, and save money!
Speak with a Cyber Risk Coordinator Today!

"After noticing unusual activity on our network, I immediately filled out the incident response form provided by ResoluteGuard. The form was straightforward and asked for all the critical details—like the time the incident was detected, the nature of the suspicious activity, and any systems affected. Our incident reports provide valuable insights that can be used to improve our cybersecurity practices."
Information Technology Director



